You’ve got something that everybody wants. What is it?
Data.
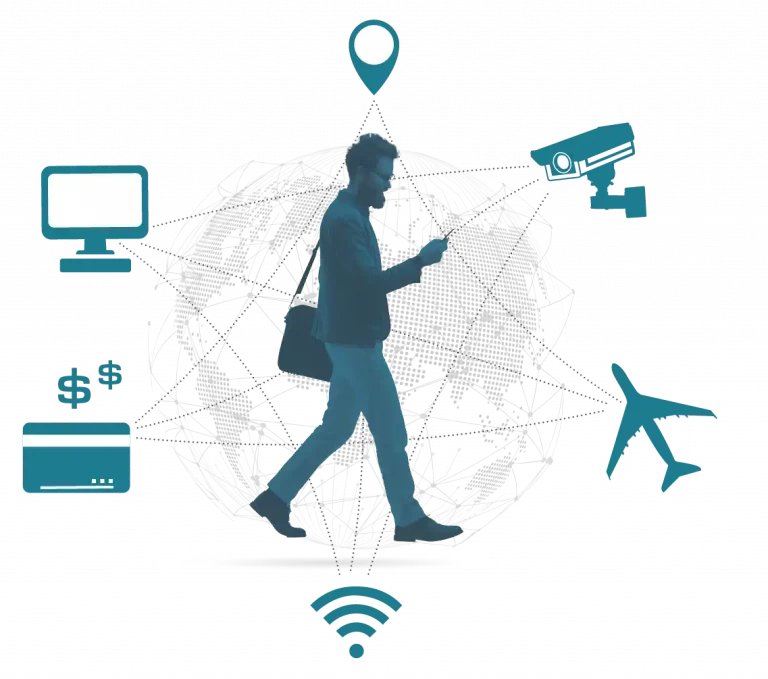
Your data is gold. Our world is designed to capture this valuable resource. Everything – our phones, our cars, our credit cards, even the streets we walk on – are collecting this data so it can be sold and stored. Your data and the associated metadata are a valuable commodity for commercial companies who use it to discover what their customers want, shape how they market that product, and serve it up in a way that will make you buy it.
What happens, though, when our adversaries use this data?
In 2017, the U.S. Government developed the concept of Ubiquitous Technical Surveillance (UTS) to describe the threat posed by governments worldwide that are escalating the use of technology to track the movements of their citizens and reconstruct their activities over time. As the ability to collect and store data became easier and cheaper, it became simpler and less expensive for adversaries to track our movements, connections, and activities.
Ubiquitous Technical Surveillance refers to the collection and long-term storage of data in order to analyze and connect individuals with other people, activities, and organizations. Because our data is stored indefinitely, these records are always accessible. In the case of Ubiquitous Technical Surveillance, this data can be used to forensically reconstruct events, no matter how long ago they occurred.
Ubiquitous Technical Surveillance is organized into five pathways for collection, also known as the five UTS Threat Vectors. Here’s a little bit of info about each one:
Online: This vector is most likely what you think about when you read or hear about data collection. Anything and everything we do online creates a fingerprint that is as unique as the ones on our fingers. The Online UTS Threat Vector includes all the data available about us online and the info generated by the devices we use to access the Internet. It’s what can be found out about us using simple Internet searches, as well as the data we generate when interacting with websites, search engines, apps, software programs, and more. From Internet browser cookies, to Advertising IDs (Ad-IDs), the Online UTS Threat Vector is a goldmine for advertisers wanting to know what you like and are searching for. Over time, this collection provides enough information to identify you based on your online habits. This fingerprint allows an advertiser to pinpoint your location, activities, and patterns, all to personalize their offers to you. Adversaries can also buy this data relatively cheaply and use what they know about your patterns to unravel hidden intentions when your activity seems outside the norm. The Online UTS Threat Vector gives adversaries insight into your use of the Internet, and since that’s where we all spend a big part of our lives these days, it paints a pretty clear picture of us.
Electronic: Before we can do all the amazing things the Internet facilitates, we first have to get connected. The Electronic UTS Threat Vector covers not just the Wi-Fi signals generated by our smart devices and the Internet of Things, but also radio frequencies (how cell phones communicate with cell towers) and telematics data created by our vehicles. This threat vector includes Bluetooth connections, GPS information, RFID, and paired devices like smartwatches or fitness trackers. It also gives adversaries a great deal of information about you, personally, like your phone’s IMEI or a computer’s MAC address. Knowing this info means that your devices can be picked out from the vast sea of other devices in the data. When you get an alert on your dash from the Tire Pressure Monitoring System (TPMS) that the air pressure in one of your tires is low, that’s data collected in the Electronic UTS Threat Vector. The IP Address assigned to your router? The info your smart thermostat sends back to its manufacturer? That data fills in just a bit more of the story about you.
Visual-Physical: Zoom in. Zoom in again. Enhance! From CCTV cameras installed by businesses, to your neighbor’s smart doorbell, the Visual-Physical UTS Threat Vector incorporates all the mechanisms that collect data about you and what you look like as you move about the world in real life. This includes more than just cameras. The Visual-Physical UTS Threat Vector also involves processing algorithms such as facial recognition and gait analysis. Data collected through the Visual-Physical UTS Threat Vector is especially useful for adversaries trying to reconstruct an event. It helps them understand who was there and what they looked like and provides evidence of the activities. Cities around the world are incorporating millions of CCTV cameras to investigate crime, deter citizens from unrest, and track the movements of everyday citizens.
Financial: Those credit card alerts sent to your phone to help prevent fraud? You’ve got data collection to thank for that. The Financial UTS Threat Vector covers the data generated by financial transactions. After 9/11, banks worldwide collaborated on counter-terrorist financing efforts. This enabled banks and governments to track all the money moving worldwide. Swiping, tapping, and inserting a card to pay, paying bills on a banking app, sending money through another app, and even writing a check that eventually gets deposited into an account – they all create a trail of data and attribution that can help keep you safe from fraud. But these actions also shed more light on your patterns and behaviors and can connect you with people or institutions.
Travel: The Travel UTS Threat Vector includes all the data created by travel activities. This includes things like flight itineraries, location searches in your GPS, connections and communication with travel companions, and more. In short, the Travel UTS Threat Vector can help adversaries identify where we go, how and when we go there, and with whom we meet when we get there.
Through Ubiquitous Technical Surveillance, our adversaries get deep insight into how businesses and government organizations operate. When overlaid, datasets from any combination of the five UTS Threat Vectors can be used to construct a vivid picture that describes your pattern of life or business operations. When these patterns are established, anomalous activities, such as those performed in government operations or routine business matters, can thwart missions or disrupt business plans.